The Identity Gap in the Age of AI Agents #
The enterprise AI revolution is no longer coming, it’s here. Organizations worldwide are deploying AI agents that autonomously access data, make decisions, and execute actions at machine speed across corporate infrastructure. Yet beneath this acceleration lies a critical blind spot: 88% of organizations have experienced suspected or confirmed AI agent security incidents, but only 22% treat agents as independent identity-bearing entities1.
This represents what Okta identifies as “the identity gap”, a dangerous mismatch between how fast AI agents proliferate and how slowly security controls adapt. While enterprises spent decades refining identity governance for employees, contractors, and partners, AI agents now operate outside these frameworks, accumulating privileged access without oversight, accountability, or audit trails.
The problem intensifies with “shadow AI”, agents employees create informally through platforms like ChatGPT Team, Claude for Work, or custom scripts calling LLM APIs. Research shows 91% of organizations already deploy AI agents, yet 44% lack governance frameworks and 23% have experienced credential exposure through agents2. These aren’t theoretical risks: unauthorized agents have accessed sensitive databases, exfiltrated confidential data, and made unauthorized API calls, all while remaining invisible to security teams.
Against this backdrop, Okta’s Showcase 2026 event on March 16, 2026, delivered a strategic response: the Agentic Enterprise Blueprint, a comprehensive framework positioning AI agents as first-class identities within the enterprise security fabric1.
The Regulatory Imperative #
As organizations deploy AI agents at scale, regulators worldwide are establishing governance frameworks. Regulations such as the EU Artificial Intelligence Act, along with emerging standards in the US, UK, and Asia-Pacific, share common requirements that directly intersect with identity management:
- Traceability: Complete audit logs of AI system decisions and actions
- Human Oversight: Mechanisms to pause, override, or revoke agent actions
- Accountability: Clear attribution of who authorized each agent and what it accessed
- Transparency: Users must know when they interact with AI systems
- Cybersecurity: AI systems must be resilient to attacks and unauthorized access
These requirements make AI identity governance a board-level compliance imperative. The Agentic Enterprise Blueprint provides the foundation for meeting these obligations through comprehensive agent discovery, lifecycle governance, and audit-ready accountability.
Okta Showcase 2026: Securing the Agentic Enterprise #
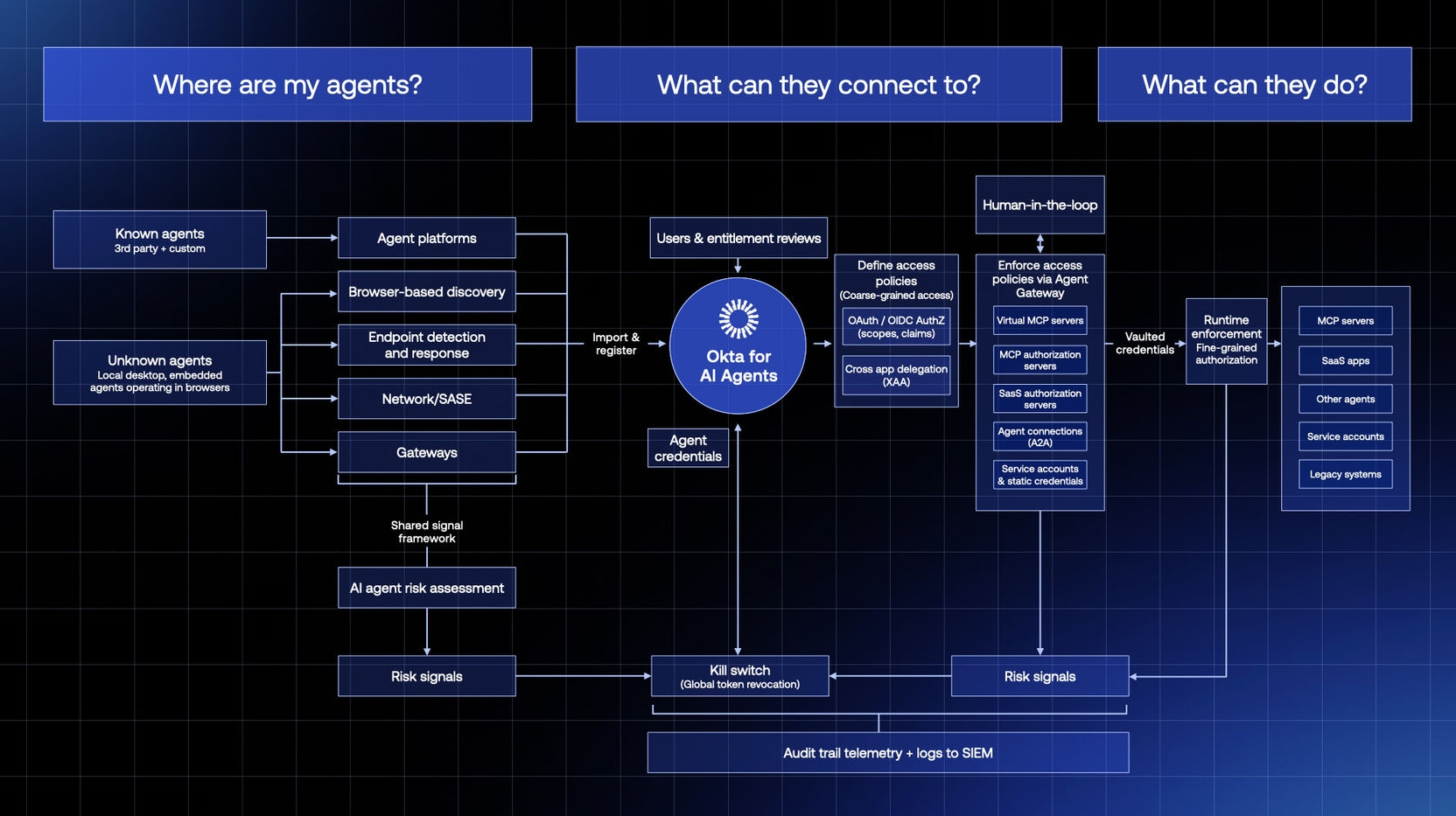
On March 16, 2026, Okta unveiled a comprehensive platform evolution designed to answer three foundational questions every CISO must address in the agentic era1:
- Where are my agents? – Establishing complete visibility across shadow and sanctioned deployments
- What can they connect to? – Mapping and controlling resource access pathways
- What can they do? – Enforcing runtime controls and behavioral policies
Major Announcements #
Okta for AI Agents (General Availability: April 30, 2026) A platform extension bringing AI agents into the enterprise identity security fabric with capabilities spanning discovery, registration, governance, and threat response13.
Auth0 for AI Agents (Early Access) Developer-focused tools enabling application teams to build secure agentic workflows with identity verification, token management, and human approval mechanisms23.
Identity Security Fabric Use Cases (Generally Available) Unified control plane integrating governance, threat protection, and privileged access across human and non-human identities3.
These announcements represent more than feature additions: they constitute an architectural shift treating AI agents as first-class identities alongside employees, contractors, partners, and service accounts.
The Agentic Enterprise Blueprint: A Three-Pillar Framework #
Okta’s Agentic Enterprise Blueprint provides a structured approach to AI agent security, built on three interconnected pillars that answer the foundational questions every security team must address4:
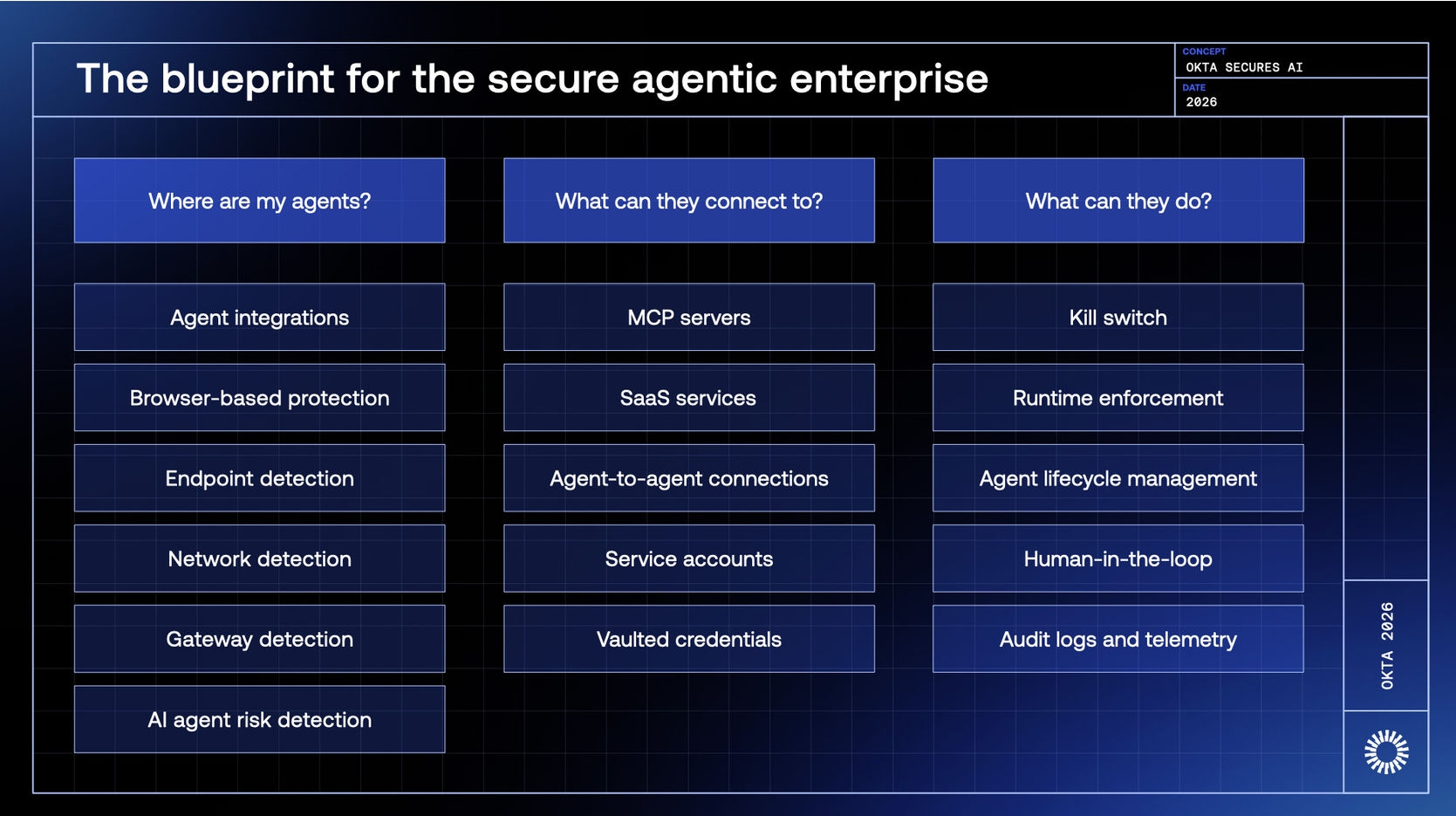
Pillar 1: “Where are my agents?” — Discovery & Visibility #
The Challenge: Shadow AI proliferates through multiple channels: employees creating custom agents via public LLMs, development teams integrating third-party agent platforms, business units deploying specialized automation tools. Traditional discovery mechanisms fail because agents don’t authenticate like humans.
The Solution: Multi-layered detection combining:
- Agent integrations: Direct registration from agent platforms like Boomi, DataRobot, Google Vertex AI, and custom systems through the Okta Integration Network
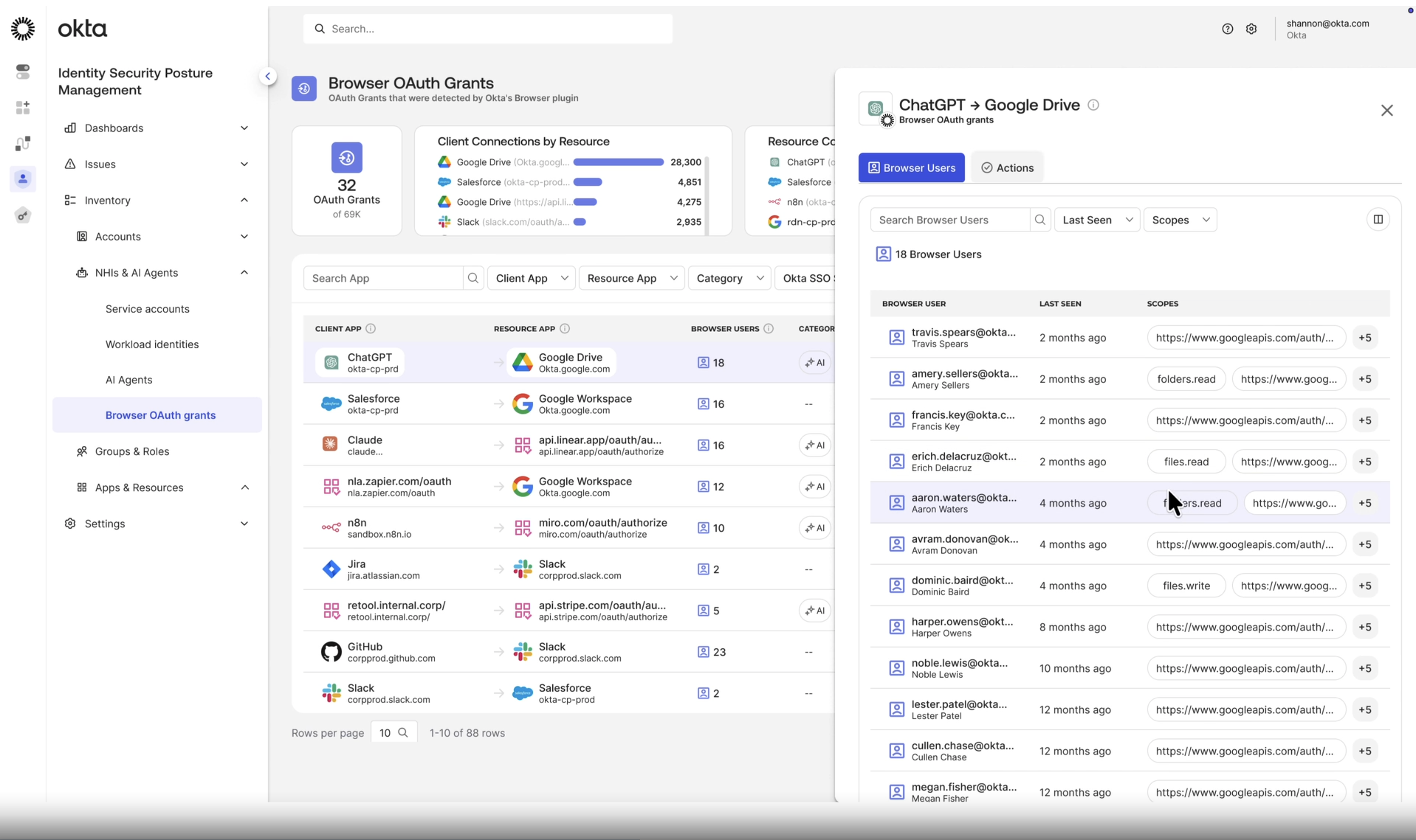
- Browser-based protection: Identifying agents created through web interfaces using Okta Browser Plugin analytics
- Endpoint detection: Discovering agents running on managed devices
- Network detection: Identifying unauthorized agent communications through SASE and network monitoring
- Gateway detection: Spotting unregistered AI clients through API gateway traffic pattern analysis
- AI agent risk detection: Automated risk assessment generating risk signals for newly discovered agents
Okta Implementation: Shadow AI Agent Discovery scans cloud environments to automatically detect unmanaged agents, flagging them for security review before registration. This addresses the 91% of organizations already deploying agents, many unknowingly, by making the invisible visible23.
Pillar 2: “What can they connect to?” — Access Control & Credential Management #
The Challenge: AI agents require access to databases, APIs, SaaS applications, and other agents to perform their functions. Traditional approaches grant agents static service account credentials, creating permanent privileged access that violates least-privilege principles and presents attractive targets for attackers.
The Solution: Dynamic credential management and centralized authorization covering all connection types:
- MCP servers: Centralized Agent Gateway aggregating access to Model Context Protocol servers for tool and data access
- SaaS services: OAuth/OIDC-based authentication to enterprise applications with scope-based permissions
- Agent-to-agent connections: Cryptographic handshakes and policy enforcement when agents invoke other agents
- Service accounts: Governance and visibility over underlying service account usage
- Vaulted credentials: Secure credential storage with automated rotation eliminating static secrets
Okta Implementation: Universal Directory now treats AI agents as distinct identity types, each with ownership attribution, approval workflows, and access policies. The Agent Gateway (leveraging MCP) provides a unified access layer where security policies apply consistently across all agent interactions34.
This approach directly supports regulatory compliance by eliminating the credential sprawl that makes traceability impossible. With credentials tied to specific agent identities rather than generic service accounts, organizations can definitively answer: “Which agent accessed this data, when, and why?”
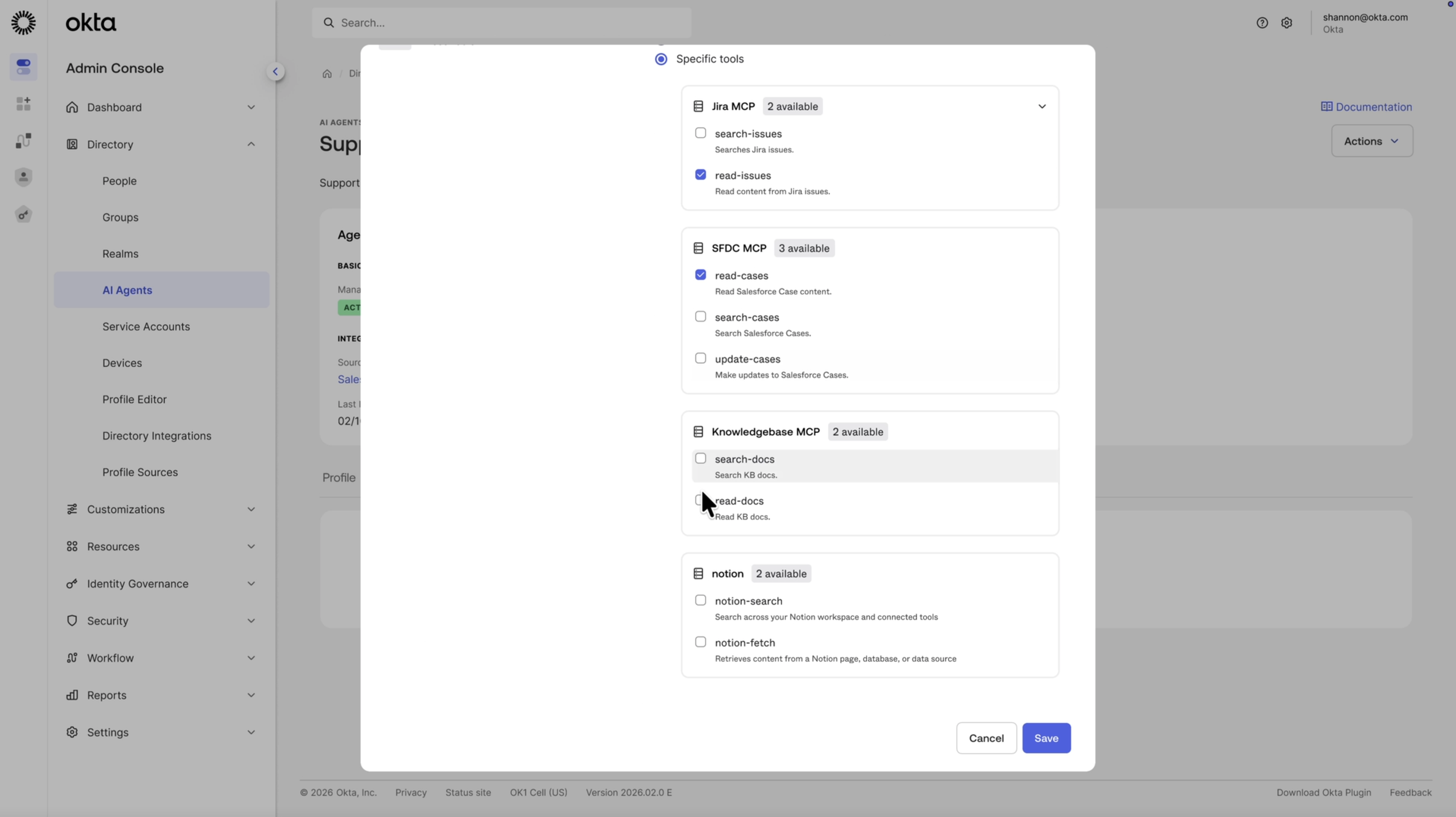
Pillar 3: “What can they do?” — Governance & Runtime Controls #
The Challenge: Without governance, agent permissions accumulate over time, following the same “privilege creep” pattern that plagues human identities. Agents created for temporary projects continue accessing resources indefinitely. Ownership changes occur without access reviews. Test agents migrate to production with excessive permissions.
The Solution: Extending Identity Governance and runtime controls to non-human identities:
- Kill switch: Universal logout capability for instant emergency response
- Runtime enforcement: Policy engine evaluating every agent action against defined rules
- Agent lifecycle management: Certification campaigns, deactivation workflows, and continuous least-privilege assessment
- Human-in-the-loop: Approval workflows pausing agent operations for sensitive actions requiring human oversight
- Audit logs and telemetry: Complete trails capturing agent actions, configuration changes, and compliance evidence
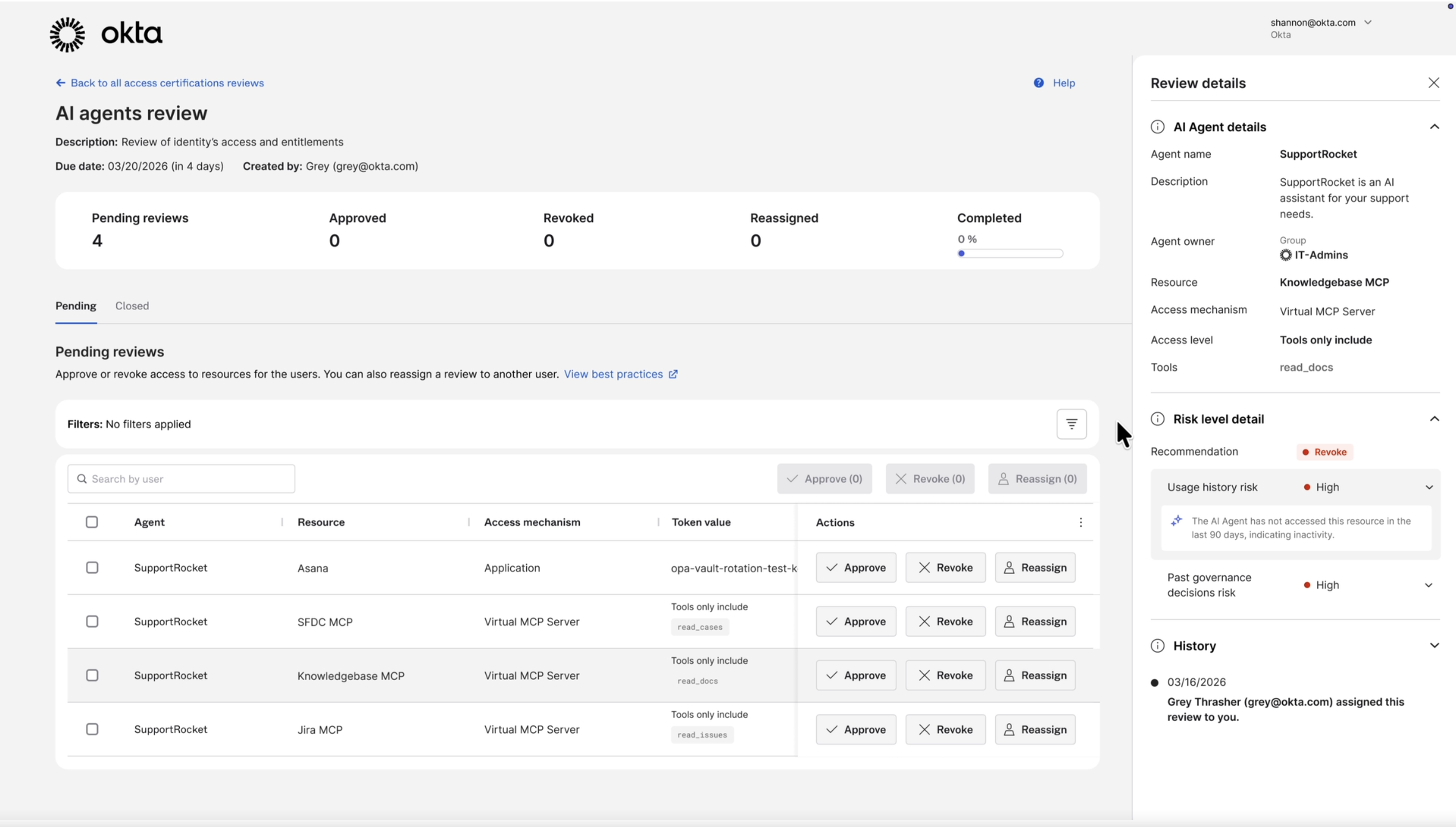
Okta Implementation: Okta Identity Governance (OIG) now includes AI agents in standard certification workflows. Security teams can launch campaigns asking: “Should the Customer Support Agent still access the Payment Database?” Business owners approve, modify, or revoke access, applying the same rigor to agents as to privileged human accounts3.
The Universal Logout capability addresses perhaps the most critical requirement: immediate threat response. If an agent exhibits anomalous behavior, like accessing unusual data volumes, making unexpected API calls, or showing signs of prompt injection compromise, security teams can instantly revoke all access while investigating13.
The Three Pillars in Action: An Integrated Architecture #
The following diagram illustrates how these three pillars interconnect through the Okta platform, with the Agent Gateway and Policy Engine at the center, processing risk signals from discovery, enforcing access policies, and enabling runtime controls including the kill switch for emergency response:
Technical Deep Dive: Okta for AI Agents #
Okta for AI Agents extends the core identity platform with capabilities specifically designed for autonomous systems34.
Key Capabilities #
1. AI Agent Registration in Universal Directory
Powered by Okta Universal Directory
Each agent becomes a distinct identity with attributes including:
- Agent name and description
- Owner/sponsor (human accountability)
- Creation date and lifecycle status
- Access permissions and scope
- Connection to underlying service accounts
- Risk score based on privilege level and behavior
This registration process answers regulatory traceability requirements: organizations can demonstrate which agents exist, who authorized them, and what they’re designed to do.
2. Shadow AI Discovery Engine
The discovery engine leverages multiple data sources:
- Cloud infrastructure APIs (scanning AWS, Azure, GCP for agent workloads)
- SaaS application logs (identifying agents authenticated to Salesforce, Microsoft 365, etc.)
- Network traffic analysis (spotting LLM API calls from unexpected sources)
- Endpoint detection (finding agents on developer workstations)
Discovered agents are flagged as “unmanaged” and enter a registration workflow requiring:
- Business justification
- Owner assignment
- Risk assessment
- Access scope definition
3. Privileged Credential Management
Powered by Okta Privileged Access
Rather than granting agents permanent credentials, Okta implements:
- Just-in-time credential provisioning: Generating short-lived tokens only when agents need access
- Automated credential rotation: Rotating underlying secrets without agent code changes
- Secure vaulting: Storing credentials in hardware-backed secure enclaves
- Usage tracking: Complete logs of credential issuance and usage
This eliminates the 23% of organizations experiencing credential exposure through agents, by ensuring credentials are ephemeral, monitored, and revocable2.
4. API Access Management Integration
Powered by Okta API Access Management
Okta’s API Access Management enforces least-privilege at runtime:
- Agents receive OAuth 2.0 access tokens scoped to specific resources and operations
- Token introspection validates permissions on each request
- Policy engine evaluates context (time, frequency, data volume) before granting access
- Anomaly detection identifies deviations from expected behavior
For example, a “Customer Support Agent” might have scope: read:customer_data, read:order_history, but explicitly lack write:payment_methods. Attempts to exceed scope are blocked and logged.
5. Certification Workflows & Governance
Powered by Okta Identity Governance (OIG)
AI agents enter the same governance lifecycle as human identities:
- Onboarding: Formal request-and-approval process
- Access reviews: Quarterly certification campaigns
- Lifecycle events: Automated deactivation when owners leave, projects end, or risk thresholds exceed
- Audit reporting: Complete trail for compliance teams
6. Universal Logout / Kill Switch
Powered by Okta Identity Threat Protection (ITP) and Single Sign-On
The emergency response mechanism revokes:
- All active sessions and access tokens
- MCP server connections
- API gateway authorizations
- Privileged credential access
This supports regulatory human oversight requirements: organizations can immediately halt agent operations if harm is detected3.
Demo Video #
See the Okta for AI Agents demo video showcasing agent discovery, registration, access control, and runtime governance in action:

Licensing & SKUs #
The Okta for AI Agents SKU bundles all the capabilities needed to govern AI agents through a unified control plane. The bundle includes use cases for:
- Identity Security Posture Management (ISPM): Shadow AI discovery
- Universal Directory: Agent registration and identity management
- Single Sign-On: Authentication and session management
- API Access Management: OAuth 2.0 scopes and token policies
- Privileged Access: Credential vaulting and just-in-time access
- Access Governance: Certification campaigns and lifecycle management
Collectively, these are referred to as “Agentic Identity Services”.
Licensing Model: The SKU is measured by Agent-to-Identity Connections, defined as a unique association between an AI Agent and a User. When a user is assigned to an AI Agent’s linked application within Agentic Identity Services, that assignment counts toward the connection total. If a user is associated with multiple AI Agents, each association counts separately.
The Advanced SKU provides increased capacity for organizations with complex agent architectures requiring multiple custom authorization servers and higher token throughput.
For complete terms, see Product Subscription Reference Guide.
Identity Fabric for the AI Era #
The Agentic Enterprise Blueprint extends Okta’s foundational Identity Fabric concept: a unified architecture governing all identity types, to explicitly encompass AI agents3.
This architectural approach delivers strategic advantages:
1. Unified Governance Model
Rather than separate systems for:
- Employees and contractors
- Partners and customers
- Service accounts and applications
- AI agents
Organizations manage all identities through a single control plane. This eliminates governance blind spots and reduces operational complexity.
2. Open Standards Foundation
The Agentic Enterprise Blueprint leverages standards including:
- OAuth 2.0 / OIDC: Authentication and authorization
- SCIM: Identity provisioning
- Model Context Protocol (MCP): Agent-to-resource access
- Shared Signals Framework (SSF): Cross-platform threat intelligence
This vendor-neutral approach prevents lock-in, enabling organizations to choose best-of-breed agent platforms while maintaining consistent security controls.
3. Future-Proof Architecture
As AI capabilities evolve, from today’s task-specific agents to tomorrow’s general-purpose autonomous systems, the identity framework remains constant. New agent types register in Universal Directory, receive scoped permissions, undergo governance reviews, and integrate with threat detection, no architecture redesign required.
4. Business Enablement, Not Obstruction
The blueprint’s goal isn’t blocking AI innovation but enabling it securely. By providing:
- Streamlined agent registration workflows
- Developer-friendly APIs (Auth0 for AI Agents)
- Automated compliance reporting
- Clear approval processes
Organizations can deploy agents confidently, knowing security and compliance are assured from day one.
Conclusions: Treating Agents as First-Class Identities #
The proliferation of AI agents represents the most significant identity challenge since the rise of SaaS applications a decade ago. Just as organizations eventually standardized on SSO and centralized IAM for cloud applications, the agentic era demands extending identity governance to autonomous systems.
Okta’s Showcase 2026 announcements: Okta for AI Agents, Auth0 for AI Agents, and the Agentic Enterprise Blueprint, which provide the first comprehensive framework treating agents as first-class identities. This isn’t simply a product evolution; it’s an architectural maturation recognizing that identity is the control plane for all enterprise interactions, whether initiated by humans, applications, or AI.
As AI regulations worldwide (such as the EU Artificial Intelligence Act) take effect, organizations face a choice: reactively bolt-on compliance after agents are deployed, or proactively build governance into the foundation. The Agentic Enterprise Blueprint enables the latter, transforming regulatory obligation into strategic advantage.
The key insight is this: AI agents are not tools; they are autonomous actors requiring the same identity rigor as employees accessing sensitive data. Organizations that recognize this fundamental shift (and implement governance accordingly) will navigate the agentic era securely, compliantly, and competitively.
Those that delay face the same credential sprawl, shadow IT proliferation, and audit nightmares that plagued early cloud adoption, except at machine speed, with AI agents autonomously accessing data 24/7/365 without visibility or control.
The identity gap is real. The Agentic Enterprise Blueprint closes it.
Getting Started with AI Agent Governance #
🎓 Get the Okta for AI Agents Early Adopters badge #

Become an AI Identity Leader: learn to evaluate AI risks and identity security gaps, and implement a comprehensive governance framework using Okta for AI Agents.
Get your Okta for AI Agents Early Adopters skills badge today!
🚀 Explore Okta’s AI Agent Capabilities #
- Okta for AI Agents: Learn about discovery, governance, and threat response for enterprise agents
- Auth0 for AI Agents: Explore developer tools for building secure customer-facing agentic applications
- Agentic Enterprise Blueprint: Download the complete framework guide
- Compliance Resources: Understand how identity governance supports regulatory requirements
💬 Join the Conversation #
How is your organization approaching AI agent security? Have you encountered shadow AI in your environment? What governance challenges keep you up at night?
Share your experience in the comments below or connect with me on LinkedIn to continue the discussion.
-
Okta Showcase 2026: Press Release, Okta Newsroom, March 16, 2026 ↩︎ ↩︎ ↩︎ ↩︎ ↩︎
-
Okta Secures AI: Solutions Overview, Okta, 2026 ↩︎ ↩︎ ↩︎ ↩︎
-
Launch Week 1: Showcase Edition - Product Announcements, Okta Product Blog, March 2026 ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎
-
The Agentic Enterprise Blueprint: A Framework for AI Agent Security, Okta, 2026 ↩︎ ↩︎ ↩︎

